What Epstein's Emails Reveal About Privacy and Power
After missing the deadline for the Epstein Transparency Act, the Department of Justice has released an additional 3M pages of Epstein’s emails and documents, many heavily redacted. They are also holding onto an additional 2.5M documents that will remain unreleased, supposedly to protect the victims.
The entire Epstein dataset is available for download from the Justice Department’s website, and eager researchers have already begun repackaging the material for easier consumption using AI tools.
In today’s piece, I used some of these AI tools to dig into this crime story at the center of everyone’s attention. Normally, I avoid topics that appear to distract from important issues, but the despicable acts of Epstein and his network have the potential to wake up millions of people.
For the first time, we are seeing how some elites conduct themselves behind closed doors—perceiving themselves as superhuman while treating their victims as property.
Blinded by his delusions, Epstein and his associates operated brazenly in the open, discussing trafficking their victims and potentially even topics like cannibalism through Gmail and Yahoo.
These platforms demand to scan the world’s photos and emails “for the children,” but they remain incredibly silent after facilitating child abuse.
Where the Emails Came From
The FBI and DOJ subpoenaed both Gmail and Yahoo—the two services Epstein used and pulled all of the emails from his accounts. According to Peter Wyatt of the PDF Association, the raw email data were extracted, converted to PDF, and then redacted before being released.
Because Epstein relied on Gmail, the archive contains attachments of child abuse images, explicit videos, and links to torture material that were sent through Google’s platform.
How Epstein Operated
Epstein himself never cultivated a personal social media profile. Instead, friends and associates would forward him posts—often pictures of women or gossip—via email or messaging services.
An associate from France was shown in the files sending screenshots of Instagram models to Epstein.
How Epstein Maintained Relative Privacy
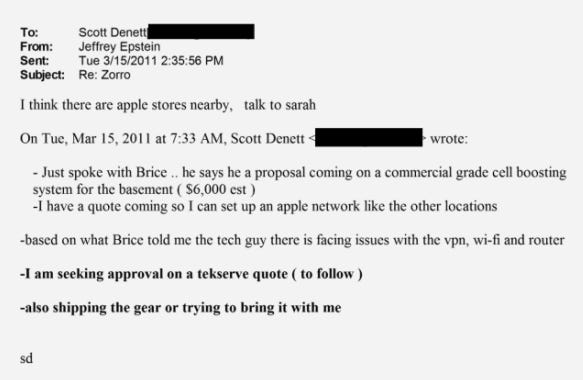
Epstein had infrastructure and computers at multiple properties, and rather than use a VPN per location, he contracted the use of a commercial-grade MPLS VPN. This type of system is typically deployed across multiple remote data centers, routing traffic between them so that they appear as part of one local network. This gave Epstein the ability to tie his various properties (Zorro Ranch, Little St. James, and his Manhattan building) together on a single local network so he could interact with each site as he was travelling.
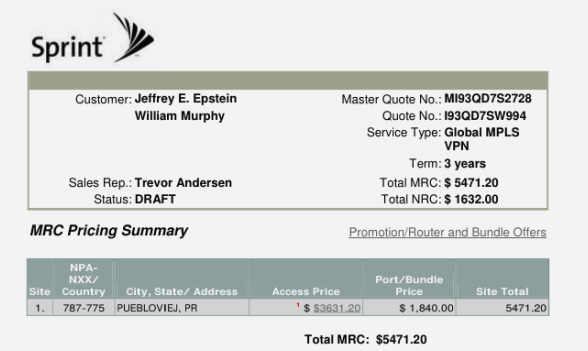
Epstein also had plans for commercial-grade cell boosters in the basement of Zorro Ranch to ensure mobile connectivity in the underground tunnels.
With minimal information leakage and social media, you could really only find Epstein if you knew his email. He kept distance from most people through his network of contacts and team that would help coordinate.
Hiding His Crimes
One of Epstein’s main activities was to procure girls, often from outside of the United States, to travel and give massages. The word “girls” is mentioned more than 30,000 times in the email trove.
Not only was Epstein requesting that his victims bring their friends, but he had brokers working overseas to identify and facilitate the trafficking of models or other young women to his many properties.
Although images were often attached to the emails themselves, Epstein most often used file transfer services (like Flip Video) to receive images and videos from his brokers.
Jean Luc Brunel, one of Epstein’s closest associates, helped him acquire models and girls from overseas. He appears frequently in the files, sending Epstein videos—presumably of different models. Brunel was arrested for sex trafficking in 2020 and mysteriously “died” in jail, exactly like Epstein.
Logistics & Supply Orders
Although Epstein bought countless things with his fortune, he usually kept his name out of it. Instead, members of his team put their names on the orders. A key person, Karyna Shuliak, handled most of the day-to-day procurement of supplies across his properties—from the snacks in the break room to the bikinis that victims were forced to wear.
Her online orders showed she arranged lodging, meals, and even costume requirements for island visits. Amazon was used extensively, purchasing everything from protein bars to DNA‑testing kits allegedly meant for “Sultans in Saudi Arabia.”
Codewords
The archive contains a bewildering 177,000+ mentions of “jerky,” which some suspect could be a euphemism for human meat. Whatever it is, it’s clear that Epstein was having large amounts of “jerky” prepared at Zorro Ranch. In the emails, these are presented as beef jerky, and Epstein seemed to be addicted to it, finishing his portions quicker than expected and getting angry and frustrated at others when he runs out.
What We Can Learn from Epstein’s (Lack Of) Operational Privacy & Security
It is quite insightful to see extreme privacy measures like co-located VPNs together with spilling major crimes over a simple email, but that’s exactly what you might expect from a well-resourced person who’s convinced they’re more intelligent than they really are.
Epstein’s connections to many big tech players (Elon, Mark, and Sergei) didn’t save him—although these platforms have not lived up to their ideals of ‘protecting kids’ and have done little to acknowledge the situation.

Despite being backed by hundreds of millions of dollars, intelligence agencies, and an extremely powerful network, Epstein couldn’t save himself from his own evil and stupidity.
The same pictures he used for blackmail now have the lights of the world shining down on them.
Like countless others, I expect nothing from our justice system. There will be no arrests or accountability for the hundreds of co-conspirators in the files; in fact, they may continue to be protected.
Don’t let this bring you down, and don’t surrender your power. We can look within for personal accountability, living a lifestyle that does not buy into, support, feed, or otherwise entertain the abusive systems that make crimes like Epstein’s possible.

Privacy phones aren’t just alternatives—they’re better than big tech.
With Above Phone, you’ll unlock features and freedom you didn’t even know existed.
- Works with any cell service (and even over WiFi with an internet phone)
- Download the apps you love (private app stores)
- Have complete control over your app permissions
Take Back Our Tech Newsletter
Join the newsletter to receive the latest updates in your inbox.





